RESOURCE CENTER
Cybersecurity
and IT Resources
Subscribe to Logically's newsletter for byte-sized cyber insights.
Search
Resource Type
Resource Topic

Cybersecurity
Blog
The State of Cybersecurity in 2026: What Modern Businesses Must Get Right
Top cybersecurity policies for 2026. Logically supports mid-market MSPs/MSSPs with smarter protection for cloud, SaaS, and hybrid work.

Blog
Why Cyber Insurance Has Become Essential in the Mid-Market
Mid-market leaders face rising cyber risks and stricter underwriting. Learn why cyber insurance is essential, what it covers, and how to strengthen insurability.

Blog
Beyond Pilot: The Strategic Framework for Scaling M365 Copilot Adoption
Learn how to effectively scale M365 Copilot adoption by focusing on business value, structured pilots, and practical training to achieve measurable productivity gains.
.webp)
Healthcare
Webinar
Logically Uncovered Webinar Series - Hacking Healthcare IT Budgets
Smarter Spend Strategies for Healthcare Mid-market Companies Navigating the 2026 Budgeting Season Budget season is here — are your IT and security priorities aligned for 2026? For healthcare mid-market companies, building a forward-looking IT budget means more than checking compliance boxes. It’s about strengthening your cyber posture, modernizing legacy infrastructure, and investing wisely in technologies that reduce risk and improve patient outcomes.Watch our webinar to learn how to shift from reactive compliance to a Cyber First strategy — where smart planning today prevents costly incidents tomorrow.

Cybersecurity
Case Study
Case Study: Cameron Mitchell Restaurants Transforms Network Infrastructure
Cameron Mitchell Restaurants, a nationally renowned restaurant group known for providing unforgettable dining experiences, faced a modern challenge: scaling secure, high-performance network infrastructure across 74 unique locations while maintaining operational excellence.
Blog
LogicON 2025 Recap: The SMB Advantage in Action
Discover key takeaways from LogicON 2025—how mid-market IT leaders are building AI readiness, digital trust, and secure business growth.

Blog
Cybersecurity Awareness Month: How to Build a Culture of Security That Lasts All Year
Cybersecurity Awareness Month is a time to practice how to remain secure all year. Follow these tips and actionable insights to increase your security posture.

Cybersecurity
Budgeting
Blog
2025 Cybersecurity Readiness Scorecard
A mid-midmarket leader's guide to high-ROI investments in cybersecurity, compliance, and operational readiness.

Blog
Windows 10 End of Life: What IT Leaders Must Prioritize Before October 2025
Windows 10 support ends October 14, 2025. Learn the risks of delaying upgrades—and get strategies IT leaders need to stay secure, compliant, and prepared.

Cloud
Blog
The Next Era of Networking: Why IT Needs a Unified Platform for the AI Age
Enterprises need unified, AI-powered networks to simplify operations and accelerate innovation. Here’s why the future belongs to platform-based IT.

Blog
Important Update: SMA100 End-of-Support and Your Next Steps
Learn how to secure AI-driven workloads at the cloud edge with unified frameworks, real-time threat detection and adaptive access controls.

Cybersecurity
Blog
Fortifying the Cloud Edge: Securing and Scaling AI-Driven Infrastructures
As organizations adopt more AI and expand cloud infrastructure to support it, a new challenge emerges: securing the “edge.”

Project Planning & Implementation
Budgeting
Blog
Make Your Final 2025 Dollars Count: How Mid-Market Firms Build IT Strength Before the Year Closes
Make your end-of-year IT budget count. Discover 7 strategic ways mid-market firms can reduce cyber risk and strengthen operations before 2026.

Cybersecurity
Blog
Preventing Business Email Compromise in Healthcare: Why IT Network Monitoring Is the First Line of Defense
With Business Email Compromise attacks accelerating in both volume and sophistication, healthcare leaders cannot rely on legacy tools or end-user discretion alone. A combination of IT network monitoring, performance monitoring, and security monitoring, underpinned by strong compliance practices, offers the best chance of avoiding serious disruption.

Cybersecurity
Blog
Updated Advisory: SonicWall Firewalls – SSLVPN Threat Activity
As of SonicWall’s latest update (August 6, 2025), the vendor has confirmed with high confidence that the observed threat activity is not the result of a new or unknown zero-day but is strongly associated with a previously disclosed vulnerability: CVE-2024-40766, detailed in SonicWall’s advisory SNWLID-2024-0015. This confirmation aligns with our internal assessments and telemetry across customer environments.

Cybersecurity
Budgeting
Blog
Budgeting for Cybersecurity: 5 Smart Strategies Every IT Leader Needs Now
Learn 5 proven cybersecurity budgeting strategies to turn IT risk into ROI, win executive buy-in, and secure the funding your team deserves.

Webinar
Logically Uncovered: Navigating Windows 10 EOL and Server Upgrades Before Budget Season
As Windows 10 nears its end-of-life in October 2025, IT and security leaders face a critical moment to align infrastructure planning with security and compliance goals. This timely on-demand webinar helps you navigate the risks of delay and prepares you to communicate urgent upgrade needs ahead of 2026 budget deadlines.
.png)
Retail
Webinar
Zero Trust in Retail: How to Protect Your Business in 2025 and Beyond
Join us for an exclusive online event where two industry leaders, Zack Finstad, VP of Cybersecurity, and Todd Barret, Director of Cybersecurity Sales, will come together to discuss the top three challenges facing the retail industry in cybersecurity. Retail businesses face a rapidly evolving threat landscape, with cyberattacks becoming more sophisticated and frequent. From securing customer data to managing supply chain vulnerabilities, the stakes are higher than ever. Don’t miss the opportunity to gain valuable insights and actionable strategies from two experts who are at the forefront of tackling cybersecurity challenges in the retail sector.

Network
Blog
FORTINET VULNERABILITY – CVE-2025-24477- FG-IR-25-026
While vulnerabilities always warrant attention, this particular issue is considered low priority for most organizations because it can only be exploited by an authenticated attacker and only under specific conditions.
.png)
Webinar
Logically Uncovered: Navigating Tariffs: What IT Leaders Need to Know to Protect Budgets and Plan Ahead
With new tariff changes shaking up the market, mid-market IT leaders are facing growing uncertainty about how these shifts could potentially impact the cost and availability of critical technology. Manufacturers are already signaling price increases to offset rising import cost which, in turn, is putting pressure on budgets and strategic planning. In this engaging panel discussion, industry experts unpack the real, as well as hidden, implications of tariff changes on IT hardware, software, and services. Learn how to evaluate the risk to your organization, what signals to watch for from vendors, and how to make informed decisions around inventory, procurement, and spending.
Cybersecurity
Healthcare
Guide
How to Build Resilient Healthcare IT
Explore practical strategies to strengthen your healthcare IT environment against disruptions and cyber threats. This ebook covers best practices for enhancing security, ensuring compliance, and maintaining operational continuity.

Cybersecurity
Healthcare
Blog
IoMT Is Reshaping Healthcare Cybersecurity. Here’s What CIOs and CISOs Must Do Next.
As IoMT adoption accelerates, so do cybersecurity risks. Learn how healthcare IT leaders can secure connected devices with resilient infrastructure, zero-trust models, and better network visibility.

Cybersecurity
Healthcare
Blog
From Phishing to Deepfakes, Here’s How AI Is Rewriting Healthcare Cybersecurity
AI is fueling a new wave of cyberattacks targeting healthcare. Discover how threat actors are using AI to bypass defenses—and what IT leaders must do now to stay protected.

Cybersecurity
Healthcare
Blog
Navigating New Rules for a New Threat Landscape
Learn why traditional HIPAA compliance isn't enough in today’s threat landscape and how resilient IT can help healthcare organizations stay secure, agile, and audit-ready.

Managed Services
Blog
Why Proactive IT Support Is a Must-Have for Mid-Market Resilience
In today’s high-stakes digital landscape, mid-market organizations face the same technology demands and cyber threats as large enterprises—yet often without the same depth of internal resources. This “stuck in the middle” reality makes resilience not just a goal, but a business imperative. And at the core of that resilience? Proactive IT support.
.png)
Managed Services
Managed Services Provider Request for Proposal Template
Get your own complimentary copy of Logically’s managed services provider Request for Proposal template.

Blog
Navigating the New Tariff Landscape: What IT Leaders Must Know to Protect Their Budgets and Strategies
Learn how IT leaders can protect budgets and plan ahead amid new tariff changes impacting procurement, strategy, and vendor relationships.

Project Planning & Implementation
Blog
Microsoft 365 for Nonprofits: Hidden Perks and Pitfalls
Inefficient Microsoft 365 licensing translates directly into wasted IT budget. This report explores industry trends, common overspending areas, optimization strategies, and real-world examples to illustrate how proactive license management can lead to significant cost savings, improved efficiency, and reduced risk.

Project Planning & Implementation
Blog
2025 Cyber Threat Landscape: Key Insights from SonicWall’s Annual Report
Explore key insights from the 2025 SonicWall Cyber Threat Report, covering ransomware, BEC attacks, and AI's role in cybersecurity, plus essential strategies for MSPs.
.png)
Cybersecurity
Blog
SecureByte Gazette: Quick Wins for Strengthening Security in 2025
As we step into 2025, cybersecurity continues to be a top priority for businesses of all sizes. At Logically, we believe in helping you stay ahead of the curve with simple, yet powerful, strategies that can make a real difference in protecting your data, systems, and overall business operations.
.png)
Project Planning & Implementation
Blog
The IT Leader’s Guide to Microsoft 365 Licensing Optimization in 2025
Inefficient Microsoft 365 licensing translates directly into wasted IT budget. This report explores industry trends, common overspending areas, optimization strategies, and real-world examples to illustrate how proactive license management can lead to significant cost savings, improved efficiency, and reduced risk.

Cybersecurity
Blog
Huntress’ 2025 Cyber Threat Report: What You Need to Know to Stay Ahead
The cybersecurity world is evolving at breakneck speed, and Huntress’ 2025 Cyber Threat Report offers a front-row seat to the action. This report dives deep into the tactics, techniques, and trends that defined cyber threats in 2024—and what they mean for 2025.
Managed Services
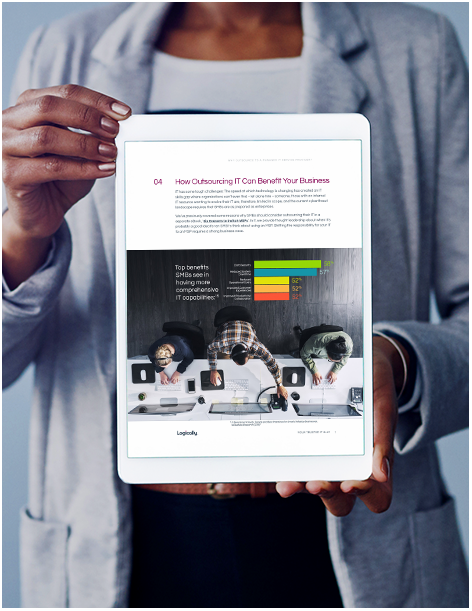
Guide
Why Outsource to a Managed IT Service Provider?
Small and mid-sized businesses (SMBs) have unique challenges when it comes to IT. MSPs help SMBs gain access to the technology that can help achieve their goals - along with the experts to manage it and keep their data secure and protected.
Compliance
Whitepaper
Security Audit & Compliance: What Every Business Needs to Know
Check out the Security Audit & Compliance e-book to learn how a layered approach to data protection—including cybersecurity technology, a compliance framework, and a knowledgeable security team—is essential to prevent data breaches and enforce regulatory standards.
Managed Services
Guide
Overcome IT Complexity: A Survival Guide for Small and Midsize Businesses
Many small to midsize business IT organizations struggle to keep pace with the constant evolution of technology in the modern business environment. Our free Survival Guide can help you understand and overcome IT complexity so that you can put technology to work for your business.
.png)
Cybersecurity
Blog
SecureByte Gazette: How to Conduct a Cybersecurity Gap Analysis
Cyber threats evolve daily, making it critical for organizations to continuously evaluate and strengthen their cybersecurity defenses. But where do you start?

Retail
Blog
Understanding Distributed Networks in Retail: Why Scalability and Reliability Matter
With the growing reliance on cloud computing, edge technologies, and a need for robust scalability, distributed networks offer a transformative solution to streamline operations across multiple locations.
-3.png)
Retail
Webinar
Logically Uncovered: Top 3 Challenges in Retail
Join us for an exclusive online event where two industry leaders, Zack Finstad, VP of Cybersecurity, and Todd Barret, Director of Cybersecurity Sales, will come together to discuss the top three challenges facing the retail industry in cybersecurity. Retail businesses face a rapidly evolving threat landscape, with cyberattacks becoming more sophisticated and frequent. From securing customer data to managing supply chain vulnerabilities, the stakes are higher than ever. Don’t miss the opportunity to gain valuable insights and actionable strategies from two experts who are at the forefront of tackling cybersecurity challenges in the retail sector. The most pressing cybersecurity challenges retail organizations are grappling with today. -Strategies to safeguard sensitive customer and business data. -Emerging technologies and solutions to stay ahead of potential threats. -Whether you are a cybersecurity professional, a retail business leader, or simply interested in understanding the intersection of retail and cybersecurity, this event is tailored for you.

Retail
Blog
Cyber Resiliency in Retail and Hospitality: Preparing for the Unpredictable
Discover the challenges retail and hospitality companies face and five of the proven approaches they can use to build their cyber resilience.

Retail
Guide
How to Overcome the Top 3 Cybersecurity Challenges in Retail and Hospitality
To ensure your business meets—or, ideally, exceeds—customer expectations, your IT teams must address three challenges that negatively impact the customer experience: complex technology environments, lack of scalability, and insufficient cyber resilience.

Retail
Blog
The Hidden Costs of IT Complexity in Retail and Hospitality
Discover the most common hidden costs of IT complexity in the retail and hospitality space and how they can ultimately affect the bottom line.

Retail
Blog
How Franchises in Retail and Hospitality Benefit from Scalable IT Solutions
Discover how scalable IT solutions can streamline franchise growth in retail and hospitality. Learn about cloud-based infrastructure, centralized management, and cybersecurity strategies to improve performance, enhance security, and support expansion across multiple locations.
Cybersecurity
Strategy
Guide
Leveraging Virtual CISO and Virtual CIO Expertise for Enhanced Cybersecurity and Technology Strategy
Virtual CIOs and CISOs (vCIOs and vCISOs) fulfill many of the same responsibilities as their in-house counterparts. However, there are several benefits to outsourcing these services to a trusted partner.
/Manufacturing%20Thumbnail.png)
Managed Services
Guide
5 Signs Manufacturers Need to Change Their MSP
When your IT partner isn’t delivering as expected, the relationship can get strenuous and in turn, affect your business. For manufacturing businesses, the landscape is getting increasingly complex with IT being an essential element of the business and having an unresponsive Managed IT Service Provider can anchor your business.
Cybersecurity
Guide
The Definitive Guide to Security Assessments: Keeping Your Business Safe in the Digital Age
Whether your organization has a mature cybersecurity program and is looking to bolster its effectiveness or your team is just beginning to explore the benefits of security assessments, learn what you need to know about these powerful evaluation tools.

Healthcare
Guide
Simplifying Security Audit & Compliance For Healthcare
The healthcare industry is faced with unique IT, security, and compliance challenges. A trusted IT ally can help health facilities identify vulnerabilities, oversee compliance requirements as well as common protocols and offer solutions as needed to meet required standards.
Cybersecurity
Whitepaper
From Challenges to Solutions: Enhancing Your SOC Through AI Integration
AI is a solution. But is it right for your SOC team? The goal of this white paper is to answer all of those questions for you. Because this isn't something you want to decide without knowing the facts.
Project Planning & Implementation
Whitepaper
Hoping for the Best, Preparing for the Worst: Why Business Continuity Planning Should Be the Foundation for Your Business
During a disaster, your company's success depends on your people and processes working without interruption. Being able to handle any crisis effectively can increase your company's value and customer confidence.

Managed Services
Whitepaper
Protecting Against Zero Day Attacks with Managed IT Services
Zero Day Attacks represent one of the greatest threats to your organization's security. During the attack, hackers find and target software vulnerabilities to gain access to your network before the associated vendor can issue a fix.
Cybersecurity
Guide
SOC Alternative Cost Calculator
Use our ROI calculator to discover how much you could save with an AI-driven SOC-as-a-Service (SOCaaS) solution.

Cybersecurity
Video
ThreatFactor
A $5 million ransom. Stolen customer data. Hacked POS devices. What caused the breach at Shutter Pro? Hear each team member’s story in the CTO’s high-stakes investigation and see if you can decipher how the threat actor got in.
Cloud
Whitepaper
Migration to Microsoft Azure: A Technical Overview
87% of organizations are planning to integrate on-premises data centers with the public cloud. But without a strong plan, risks can include a complex and time-consuming migration process compounded by lack of relevant skills, loss of control from moving computer resources off-premises, bandwidth issues, and unexpected costs. Learn how to create a strong roadmap to help your organization run in the cloud.

Compliance
Project Planning & Implementation
Guide
Copilot for Microsoft 365 Guide
Learn more about Microsoft Copilot, including the benefits of integrating AI with Microsoft 365, five productivity outcomes, security and compliance considerations, and what the future looks like for Copilot.
.png)
Project Planning & Implementation
Microsoft Copilot Readiness Checklist
Our checklist covers everything you need to know about Copilot, including how it can immediately deliver for your business and how your employees can leverage its functionality to boost productivity to improve work quality.
.png)
Project Planning & Implementation
Blog
Microsoft Insights: A Phased Approach for Onboarding AI Tools
In today’s rapidly evolving digital landscape, leveraging AI tools like Microsoft 365 Copilot can significantly enhance productivity and streamline workflows. However, the successful integration of such advanced technologies requires a strategic approach to training and onboarding.
.png)
Cybersecurity
Blog
How Brute Force Attacks Target Firewalls
In today's digital landscape, cybersecurity threats are constantly evolving, and one of the most persistent dangers organizations face is brute force attacks.

Cybersecurity
Managed Services
Blog
Scaling Your Cybersecurity: A Roadmap for Small Businesses
Discover how small businesses can scale securely with simplified tech stacks, proactive cybersecurity measures, and strategic planning.
-2.png)
Cybersecurity
Webinar
Logically Uncovered: Firewall Protection
Join Logically’s cybersecurity experts VP of Cybersecurity, Zack Finstad, and Network Security Manager, Kyle Sandy, for an insightful webinar designed to help you fortify your network against threats and protecting your firewall from increased brute force attacks.
Project Planning & Implementation
Blog
Microsoft Teams 2025: What's New?
Microsoft Teams continues to redefine how we collaborate and work effectively in hybrid and remote environments. With its 2025 updates, Teams introduces a suite of new features designed to enhance productivity by streamlining workflows, fostering collaboration, and saving precious time. Here are the top 5 features that promise to make a real impact on workplace efficiency.

Cybersecurity
Webinar
Logically Uncovered: Market Horizons
Join us for an exclusive fireside chat with Josh Skeens, CEO of Logically, as he shares his expert insights on the current market landscape and forecasts for 2025.

Cybersecurity
Blog
Important Security Notice: Protect Your Firewall from Increased Brute Force Attacks
At Logically, we’re always monitoring emerging cybersecurity threats to help keep your business safe.

Cybersecurity
Strategy
Blog
Cybersecurity Trends in 2025
Is your cybersecurity strategy ready for 2025? Learn the trends and best practices to protect your business in our latest newsletter.

Compliance
Cybersecurity
Strategy
Blog
Cyberinsurance Explained: Essential Insights for IT and Business Leaders
Explore the critical role of cyber insurance in protecting organizations, backed by data-driven insights and actionable strategies for IT and business leaders.
.jpeg)
Cybersecurity
Blog
What Is ZTNA, and How Does It Work?
Explore the myths of Zero Trust Network Access (ZTNA) for businesses, and how ZTNA enhances security by verifying identity and device health.

Cybersecurity
Case Study
Case Study: Ransomware Remediation for a Charity Organization
When a ransomware attack took down a charity organization’s entire network, Logically stepped in to provide an immediate, multi-pronged response. This case study explores how Logically addressed fragmented IT systems, inadequate backup coverage, and outdated infrastructure, restoring operations and guiding the organization toward a stronger cybersecurity posture.

Collaboration
Webinar
Logically Uncovered: Copilot in Action: From Promise to Performance in Your Microsoft 365 Tenant
In this webinar, understand the power of Microsoft's Co-Pilot and unlock the full potential in your organization.

Budgeting
Webinar
Logically Uncovered: Strategic Budgeting and Planning for IT Leaders in 2025
In this webinar, learn best practices for budgeting and planning as we approach the critical 2025 refresh cycle.
Network
Webinar
Logically Uncovered: Network Fabric, Segmentation & How They Stop a Serious Security Incident
In this webinar, learn how fabric architectures are shaping the future of cybersecurity and why segmentation is essential to that evolution.

Cybersecurity
Guide
Elevating Your Security Posture: A Guide to the NIST Cybersecurity Framework 2.0
Read the whitepaper today.
Cybersecurity
Strategy
Guide
Mitigating Modern Threats: How Zero Trust Solutions Bolster Your Security Posture
Read the whitepaper today.

Strategy
Guide
Microsoft Windows Server 2012 & 2012 R2 Brief
Download our brief for details about upcoming technology end-of-support schedules and uncover steps for creating your refresh process.
Network
Webinar
Logically Uncovered: PSTN and ISDN Changes & Their Impact on Your Telecom Budget
In this on-demand webinar, we delve into the Public Switched Telephone Network (PSTN) and Integrated Services Digital Network (ISDN) changes.

Cybersecurity
Whitepaper
The Modern SOC: How to Leverage AI-Based SecOps and Quantify the Value of Cybersecurity
Download this white paper to learn how and why to include AI in your SOC, SecOps, and cybersecurity strategies

Cybersecurity
Webinar
Logically Uncovered: Navigating Zero Trust
Join our webinar to learn about zero trust, including its principles, roles in cybersecurity, and contrast with traditional security controls.

Managed Services
Case Study
SentryXDR Helps the Education Sector Maintain Compliance with Frequently Changing Regulations
Logically's SentryXDR helps educational institutions maintain compliance and combat cyber threats. Download the case study to read more.

Cybersecurity
Logically Speaking
Ep. 4 – Asset & Data Management in “The Disposable Era”
Know the chain of responsibility when it comes to data and asset management in this episode of Logically Speaking with guest, Aaron Zeper, CEO of DMD Systems.

Cybersecurity
Logically Speaking
Ep. 3 – Building Business Continuity & Resilience
In this episode of Logically Speaking, learn threat actor TTPs hitting SMBs and the recovery process to maintain business continuity.
Cybersecurity
Logically Speaking
Decoding Cybersecurity: The Nuances of Securing Tech
Join the interview with Matt Lee at BlackHat 2023 where he decodes cybersecurity by taking a look a the history of technology.

Cybersecurity
Logically Speaking
Ep. 2 – Trained to Protect: Creating a Culture of Security
We're welcoming cybersecurity awareness month with former Pentester and current CEO of HacWare, Tiffany Ricks who shares insights on security culture.
Network
Webinar
Enhancing Network Security with CylanceOptics: From Detection to Response
Learn about CylanceOptics EDR during this on-demand webinar. Discover key requirements, significance and advantages of using Optics.

Cybersecurity
Logically Speaking
Ep. 1 – Effects of Compromise: Incident Recovery and Data Sharing
We're back with Season 2 and Former FBI special agent, Michael Anaya, shares insights on business compromise, pre and post breach.
Managed Services
Guide
Whitepaper
How to Manage the Complexity of SecOps in the Age of AI
Read the whitepaper today.

Cybersecurity
Logically Speaking
Ep. 6 – Top Tips for Reducing Cyber Risk with Suroop Chandran at SonicWall
In this week's episode, special guest Suroop Chandran from SonicWall, shares threat intelligence insights and top tips for reducing cyber risk.

Cybersecurity
Logically Speaking
Ep. 5 – Securing SLED: Cyber Challenges and Resilience
In this week's episode, special guest Craig Bowman from VMWare, shares insights on cyber attacks targeting government and education sectors.

Cybersecurity
Logically Speaking
Ep. 4 – Unveiling the Future of Cybersecurity
Logically Speaking Ep. 4: Chris Novak will teach you how to protect your business from cyberattacks in today’s rapidly evolving threat landscape.

Cybersecurity
Logically Speaking
Ep. 3 – Insights from a Ransomware Negotiator
Logically Speaking Ep. 3: Ransomware negotiator Kurtis Minder shares tips to protect your business against ransomware.

Managed Services
Logically Speaking
Ep. 2 - The 2023 Cyber Threat Landscape
Logically Speaking Ep. 2: Hear information security entrepreneur Caleb Barlow explore the current threat landscape facing mid-market businesses.



Managed Services
Guide
Whitepaper
Why Outsource to a Managed IT Service Provider eBook
Read the whitepaper today.

.jpeg)

Managed Services
Guide
Whitepaper
Partnering with an MSP to Deliver Impactful IT Projects
Read the whitepaper today.

Managed Services
Guide
Whitepaper
The Business Case for Device as a Service
Read the whitepaper today.

Managed Services
Guide
Whitepaper
Six Reasons to Switch Managed Service Providers
Learn how to tell if your specific MSP is missing the mark, as well as what questions to ask prospective MSPs you’re considering as your next choice.

Cloud
Whitepaper
Defining Your Journey to the Cloud
Download this white paper to learn how organizations look to move to the cloud and what the process of moving to the cloud looks like generally.

Managed Services
Guide
MSP Buyer's Guide
This IT MSP Buyer’s Guide will help you leverage technology to achieve your goals and take the pain out of IT.

Cybersecurity
Logically Speaking
Ep. 1 - Secure by Design: Building Safe Applications
Logically Speaking Ep. 1: The hosts discuss DevSecOps, application security, and the integration of AI to help identify pre-zero-day vulnerabilities.

Cybersecurity
Webinar
Understanding Cyber Insurability Requirements
Learn how to protect your business with cyber insurance during this webinar. Discover key requirements like MFA, EDR/MDR/XDR, and more.

Cybersecurity
Webinar
Why Application Security is Crucial in Today’s Digital Landscape
Protect your business from cyber threats with tips and strategies on application security, MFA, cloud security, Office 365, and SaaS Alerts.

Cybersecurity
Webinar
How Risk Assessment Results Help Optimize Cyber Insurance Coverage
Optimize your cyber insurance coverage based on risk assessment results. Watch this webinar for next steps and how to update your policy.
Cybersecurity
Webinar
AMA - How to Clean Up Your Data Nightmares Webinar Watch
During this AMA session, we'll take your data nightmares and show you how to clean them up to make the data work for you.
Cybersecurity
Webinar
AMA – The Difference Between Office 365 & Microsoft 365 Licensing Webinar Watch
The Microsoft ecosystem can be (and typically is) confusing by nature. In this AMA, our team speaks to the “gotchas” that can arise.

Cybersecurity
Webinar
AMA – Cyber Insurance – Understanding Insurability to Protect Your Business Webinar Watch
Watch this ask-me-anything session to learn how cyber insurance helps businesses plan for the worst but anticipate the best outcome from a cyber attack.

Cybersecurity
Webinar
AMA – Governance and Compliance – The Foundation of Reliable and Mature Cybersecurity Webinar Watch
Watch this ask-me-anything session to learn how governance and compliance contribute to a reliable and mature cybersecurity defense posture.

Cybersecurity
Webinar
The Difference Between EDR, MDR, & XDR, and Why You Need Them
Watch this ask-me-anything session, in which security experts discuss the differences between EDR, MDR, and XDR and how each tool can benefit your business

Cybersecurity
Webinar
Cybersecurity Awareness Month SonicWall Cyber Threat Report: Mid-Year Update
Cybersecurity and operations leaders from Logically and SonicWall discuss the most impactful findings from SonicWall’s "Mid-Year Threat Report."

Cybersecurity
Webinar
Cybersecurity & Insurance is Top of Mind to All Your Clients Watch Webinar
Tune in with the Logically and its partners, DataStream Insurance and TCG, for an in-depth discussion about cybersecurity and insurance.
Network
Webinar
Combating Supply Chain Issues with Device-As-A-Service Watch webinar
Watch this on-demand webinar to learn how businesses can combat supply chain issues with device-as-a-service solutions.

Cybersecurity
Webinar
EDR and SIEM-SOC Webinar
In this webinar, we will review the importance of having an Endpoint Detection and Response -EDR- solution and a SIEM SOC solution in place.

Strategy
Webinar
Making the Most of Logically as Your IT Utility Belt
Watch this on-demand webinar to learn how to get the most out of Logically’s services and solutions.

Managed Services
Webinar
Smarter Telecom with Logically
Join our webinar for a deep dive discussion on telecom, how to choose from a wide variety of different carriers, prioritize options, and save money.

Cybersecurity
Webinar
Avoiding the Phish Bowl
Phishing emails are the easiest way for cyber criminals to get into your environment. This webinar will review best practices for phishing.
Cybersecurity
Webinar
Why Threat Detection Has Become Just as Important as Prevention
This webinar is a deep-dive discussion on the shifts in the cybersecurity landscape that continue to cause the increased focus on detection and XDR.

Managed Services
Video
Backup & Disaster Recovery
In this video, we cover the essentials of backup and disaster recovery and how an MSP can help.

Cybersecurity
Video
Monitoring & Alerting
Discover how Logically’s remote monitoring and alerting services immediately detect problems in your infrastructure.

Managed Services
Video
Are Your Passwords Safe?
Are your passwords safe? Watch this video to learn how dark web monitoring can help you answer that question.

Data Center
Video
Helpdesk
Logically's help desk technicians bring industry-leading knowledge and expertise to troubleshoot and resolve technical issues.

Managed Services
Video
About Logically
Logically’s cyber-first, future-ready services and solutions stand out in the MSP space. Find out what makes us different.

Compliance
Case Study
Logically Elevates County Government IT From Fragmented to Unified
Read the case study to learn how Logically helped a local government unify its IT infrastructure across departments.

Compliance
Case Study
Gaston County’s HIPAA Security Risk Assessment Journey
Read this case study to learn how Logically helped Gaston County assess its HIPAA security risk.
Project Planning & Implementation
Case Study
Global Endowment – Preparedness and Activation During Crises
Logically’s scalability and adaptability make it the right MSP for Global Endowment Management. Read the case study to learn more.

Cybersecurity
Case Study
Insurance Company Rests Assured With Logically
Download this case study to discover why INSURLYNX selected Logically to handle its day-to-day IT operations and cybersecurity.

Cybersecurity
Case Study
Logically Provides Law Firm with Security and Peace of Mind
Read the case study to learn how Logically helped a law firm transform its data security strategy.

Managed Services
Case Study
Logically Keeps Dental Group Smiling Through Ongoing IT Support
Download this case study to learn why La Costa Dental Group chose Logically to support its secure server, desktops, and dental management software.

Compliance
Case Study
Senior Living Organization Relies on Logically for Expansion and Support
Discover how Logically helped Maplewood Senior Living implement a cohesive IT strategy across all locations that includes integrated custom technologies.

Cloud
Case Study
Morgan Creek Management – Virtualization in the Cloud Enables Seamless Remote Work
Read the case study to learn how Logically helps Morgan Creek Management support its remote workers in the cloud.
Managed Services
Case Study
Nuventra - Positioned for Continued Growth
Download the case study to learn how Logically ensures employees at Nuventra, Inc. have secure remote access to essential applications and data.

Compliance
Case Study
A Leading Global Manufacturer, Supports Enhanced Security and M&A Growth with Logically
Download this case study to learn why Allen and Coles Moving Company chose Logically to support its security, hardware, and IT infrastructure.

Compliance
Case Study
Logically Moves Acclaimed Moving Company to Continued Success
Download this case study to learn why Allen and Coles Moving Company chose Logically to support its security, hardware, and IT infrastructure.

Strategy
Case Study
Logically Builds IT Confidence for Family-Owned Building Product Company
Download this case study to learn why Nystrom partnered with Logically to set up and secure its remote workforce.

Cybersecurity
Webinar
Cisco Solutions for Your Business Webinar
Watch this to learn how Cisco solutions can help your business's webinar needs.

Managed Services
Video
Intelligent MSP Platform
Discover the benefits of OpLogic, Logically's self-healing intelligent MSP Platform that identifies and addresses IT issues before they become problems.

Cloud
Video
The Power of OpLogic
OpLogic is Logically’s intelligent MSP platform for SMBs. Learn more about OpLogic’s reliable, effective, and personalized service delivery here.
Cloud
Cloud Assessment
Most businesses are already using some form of cloud computing, such as IaaS, PaaS, or SaaS. Sign up for your assessment today.

Cybersecurity
Video
Cybersecurity Protection at Every Level with SecureCare
Take a closer look at how SecureCare’s next-gen threat protection defends against rapidly evolving ransomware, zero-day attacks, and other threats.
.jpeg)
Cybersecurity
Strategy
Security Assessment
Learn more about the benefits of Logically’s security assessments and schedule yours today.

Collaboration
Video
Managing Remote Work with the Intel vPro Platform
Mike Williams, CSO at Logically, talks about how the Intel vPro platform delivers capabilities that transform computing endpoints into more trustworthy and well-maintained productivity tools.

Cloud
Webinar
Defining Your Organization’s Path to the Cloud
Watch this on-demand webinar to learn why and how organizations are moving essential operations to the cloud.

Cybersecurity
Webinar
A Layered Approach to Security
Learn more about Huntress Labs, a security platform that helps organizations minimize their risk for cyberattacks.

Cybersecurity
Webinar
Business Value Creation and Acquisition in the World of COVID Webinar
Check out our webinar to understand the business value creation and acquisition in a post-pandemic world.

Cybersecurity
Webinar
Making Hackers Earn Their Access
In this webinar, an ex-NSA operator shows exactly how hackers target victims, compromise computers, and what they can do with little effort.

Strategy
Webinar
Creating Your Disaster Recovery and Incident Response Plan
A Disaster Recovery and Incident Response plan is a critical part of your security strategy. Are you prepared for a breach or cyberattack?

Compliance
Webinar
The Fear Factor
Security is a top priority for organizations today. This webinar will help organizations improve their security posture.

Cybersecurity
Webinar
Application Security
This webinar, Aaron Scurlock uses his over 15 years experience in IT management reviewing the elements of application security within your environment.

Project Planning & Implementation
Webinar
How Not to Be a Victim
In this webinar, we review the basics of security training and how not to be a victim of a breach or attack. This webinar is presented by Tyler Booker, Senior Auditor, at Logically.

Project Planning & Implementation
Webinar
CIS Risk Assessment Methodology
In this webinar, we review the Risk Assessment Methodology as directed by CIS. This webinar is presented by Greg Manson, Vice President of Security, Audit, and Compliance at Logically.

Collaboration
Webinar
Team Up: Using Microsoft Teams
Watch this on-demand webinar to learn why Microsoft Teams is a top choice for businesses that need a reliable, scalable collaboration tool.

Collaboration
Webinar
Best Practices for Working Remotely
This webinar will review the basics of remote support to ensure your users are prepared to work remotely in a secure manner.

Strategy
Webinar
The Benefits of Security Training
Watch this on-demand webinar to learn common cloud misconceptions, how to prioritize cloud services, and tips to successfully move to the cloud.

Collaboration
Webinar
Surviving COVID-19: Creating a Healthy Work Life Balance
In this webinar, you learn some coping skills to maintain a healthy work-life balance.
Managed Services
Strategy
Webinar
Three Reasons Why You Should Outsource Your IT
Learn about the challenges of managing technology and why you should consider outsourcing to an MSP.

Cloud
Webinar
Untangling the Cloud for Your Business
Watch this on-demand webinar to learn common cloud misconceptions, how to prioritize cloud services, and tips to successfully move to the cloud.

Strategy
Webinar
Team Collaboration in the Cloud
Watch this on-demand webinar to learn how Microsoft Teams can bridge communication gaps in your remote workforce.

Managed Services
Strategy
Webinar
Six Reasons it May Be Time to Switch IT Service Providers
Watch this on-demand webinar to learn common cloud misconceptions, how to prioritize cloud services, and tips to successfully move to the cloud.

Cybersecurity
Video
Get Insight into Your Security Posture with a Security Risk Assessment
Learn how a security risk assessment provides a deeper understanding of your business' security posture.
Sorry! There weren't any results for that filter, please try something different
Looking For a Trusted Ally?
Speak to one of our experts and learn how Logically can solve your security and IT problems.
