
SonicWall
Get an edge on emerging threats with next-generation cybersecurity, including firewall security, secure mobile access, and zero-trust network access services and solutions.

Escalating Risk of Cyberthreats
Remote and hybrid workplaces, rapidly evolving cyberthreats, and increasingly complex IT environments are changing how businesses approach security and connectivity.
Logically and SonicWall work together to deliver elite-class managed solutions and services for firewalls, secure mobile access, and wireless environments so you can defend your business systems and data on-premises, in the cloud, and everywhere in between.
Here are some 2023 global attack trends:
- 140 million ransomware attacks
- 2.7 billion malware attacks
- 3.7 trillion intrusion attempts
Cyber Threat Protection Challenges and Common Concerns
Your data is at risk 24/7/365. Logically and SonicWall help organizations in diverse sectors establish a strong cybersecurity posture, mitigate risks, and protect their critical assets and sensitive information from evolving cyberthreats.
Unauthorized Access
- Malicious actors obtain sensitive information, such as customer data, intellectual property, or financial records.
- Network resources are exploited, causing disruptions, data manipulation, or the injection of malicious code into the network.
Malware and Viruses
- Disruption to business operations results in downtime, loss of productivity, and expenses associated with system restoration and recovery.
- Exploiting vulnerabilities allows unauthorized access to sensitive information and creates a gateway for additional cyberthreats.
Intrusion Attempts
- Unauthorized access to proprietary business information, financial records, or customer data increases the risk of data breaches and regulatory non-compliance.
- Compromised access can be used to install backdoors, allowing persistent unauthorized access to the business network.
Unsecured Remote Access
- There is an increased risk of brute force attacks or man-in-the-middle attacks, which lead to data interception and manipulation or injection of malicious code into the business network.
- Outdated protocols and encryption standards create weaknesses that make it relatively easy for attackers to decrypt VPN traffic.
Advanced Email Threats
- Sophisticated phishing attacks impersonate legitimate senders, tricking employees into divulging sensitive information, such as login credentials or financial account details.
- Malicious attachments and links in emails deliver malware payloads that compromise the security of business networks and systems.
Wireless Network Security
- Rogue access points are used to intercept and manipulate data or launch further cyberattacks.
- Weak or easily guessable Wi-Fi passwords are exploited by attackers to gain access to the business network, putting sensitive data and resources at risk.
Secure Your Perimeter with SonicWall and Logically
With more than 30 dedicated cybersecurity and SonicWall-focused engineers on staff, Logically houses more expertise on SonicWall Secure Mobile Access technology than any other organization in the world outside of SonicWall.
Logically + SonicWall =
- Over 5,000 firewalls under management
- Over 8,000 SonicWall products deployed
- Over 200 Secure Mobile Access appliances under management

Balancing Productivity and Security
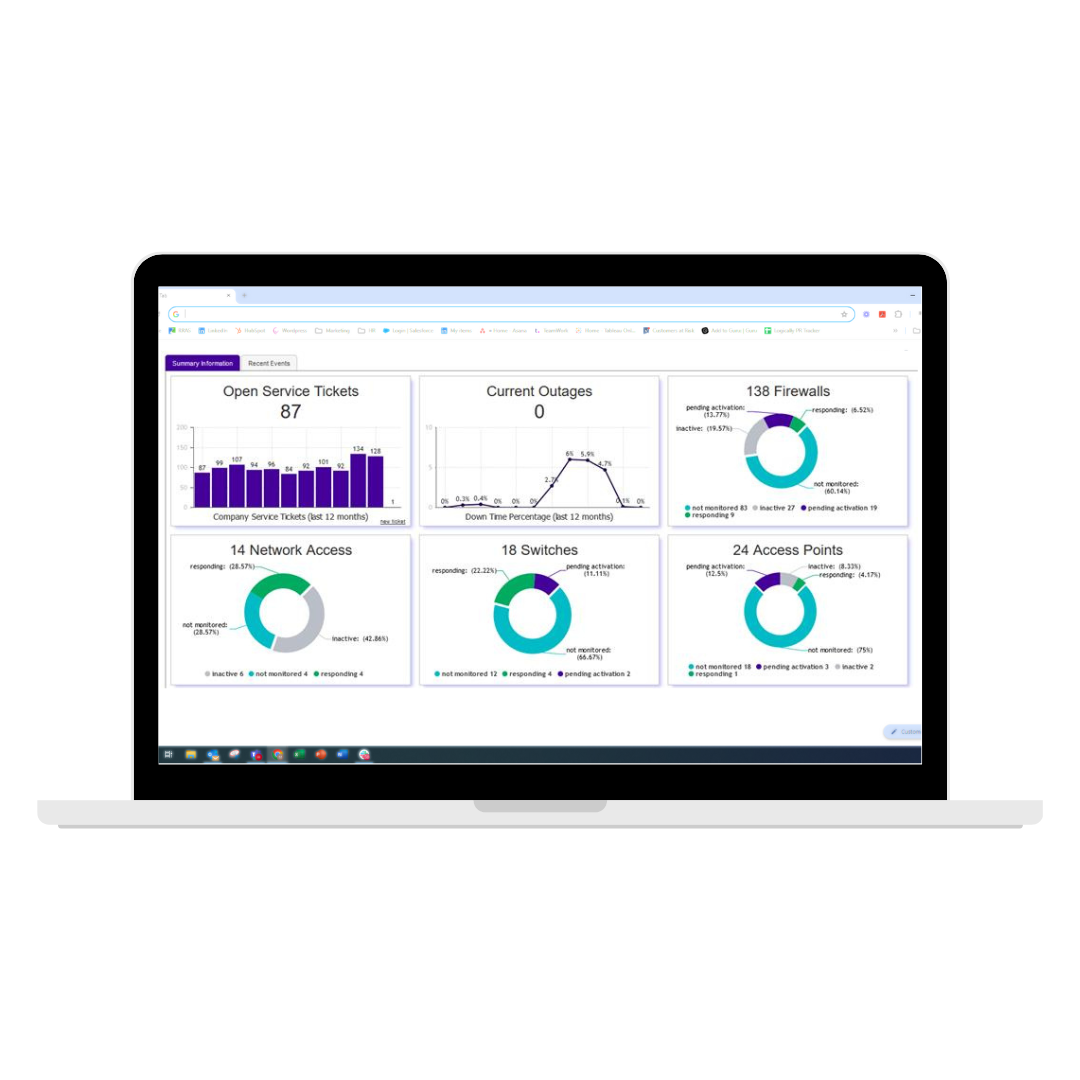
Custom Reporting Functionality
Unlike other solutions that make you add on reporting and monitoring capabilities, Logically includes custom-developed internal systems that allow you to manage and monitor SonicWall firewalls and reduce the overall cost of providing enterprise-level firewall management and network visibility to your organization.
The Pervidio cloud reporting engine was written from the ground up by the Logically development team to provide reporting and analytics specifically on SonicWall logs.
This fully web-based management and monitoring platform provides:
- 24/7/365 network uptime monitoring: With automatic alerting to both Logically and your designated response personnel, the recovery process can start immediately, reducing mean time to repair. All status and progress updates are tracked through this system.
- Automated firewall security audits: Weekly automated firewall reviews look for configuration changes that may negatively affect your security posture. If the audit identifies a problem, engineering will contact you and begin remediation.
- Nightly firewall configuration backups: Configurations are stored for a rolling 30-day period, not only eliminating the need to manage and store backups but also creating a safety net for device failure recovery and the ability to roll back damaging configuration changes.

Managed and
Co-Managed Firewall Services
SonicWall’s advanced firewall technology and Logically’s cybersecurity expertise put a highly effective barrier between your data and existing and emerging threats. With managed and co-managed firewall services, our specialists provide everything from initial configuration deployments to firmware upgrades, automatic backups, weekly system configuration audits, and more.

Secure Mobile Access
In today’s cloud-based remote business environments, SonicWall Secure Mobile Access (SMA) gateways provide peace of mind by offering granular access control, context-aware device authorization, application-level VPN, and integration with advanced authentications so that users can access applications anywhere, at any time, and from any device.

Zero Trust Network Access (ZTNA)
Legacy infrastructure wasn’t designed to handle today’s cyber threats. SonicWall’s addition of identity-centric Secure Service Edge (SSE) modernizes security architecture so it adheres to the principles of Secure Access Service Edge (SASE) frameworks and supports an industry-leading ZTNA solution that secures access to applications and resources from anywhere.

Email Security
SonicWall’s Email Security Appliances protect your organization from advanced email threats, including ransomware, phishing attacks, business email compromise, and email fraud. This multilayered solution provides comprehensive inbound and outbound protection with easy deployment, management, and reporting.

Firewall Security Consulting
Logically’s SonicWall specialists are available to conduct an end-to-end evaluation of your firewall, looking for misconfigurations and other risk vectors. You will receive a full report of the findings and a capture threat assessment report that provides global threat data, activity data gathered during the reporting period, and historic data about the firewall's functionality.

Professional Services
Need a hand getting a firewall installed, configured, and deployed? Logically’s experts will work with your team to migrate from an older firewall to a newer version or design and deploy an initial firewall based on your network data. We do a full build and configuration from the ground up, and you get a plug-and-play solution built to Logically’s highest security service standards.
SonicWall’s acquisition of Banyan Security enables Logically to help customers implement a powerful ZTNA solution that seamlessly extends their on-premises security capabilities to encompass cloud and hybrid environments, remote employees, and bring-your-own-device (BYOD) scenarios.
” SonicWall’s steadfast commitment to not just maintaining, but growing their security efficacy year over year empowers Logically to confidently protect thousands of customer networks.
And the Awards We Reap








Looking For a Trusted Ally?
Speak to one of our experts and learn how Logically can evolve with your business needs while managing the complexity, performance, and security of your business technology.



/Upgrading%20firewalls-1.jpeg?width=1200&height=685&name=Upgrading%20firewalls-1.jpeg)








